 This is a continuation of my blog post on intro to digital watermarking. In that post, we discussed what digital watermarking is and how it can be achieved. Here, we will discuss the intuition behind image watermarking and a few techniques that can be used. If you look at enough number of images, you will realize that not all of them are equally suited for watermarking. At least, we cannot use the same criteria to watermark all the images. How do we know where to watermark an image? Are there any rules or do we just place some watermark randomly in an image? Does it make a difference? Continue reading “The Intuition Behind Image Watermarking”
This is a continuation of my blog post on intro to digital watermarking. In that post, we discussed what digital watermarking is and how it can be achieved. Here, we will discuss the intuition behind image watermarking and a few techniques that can be used. If you look at enough number of images, you will realize that not all of them are equally suited for watermarking. At least, we cannot use the same criteria to watermark all the images. How do we know where to watermark an image? Are there any rules or do we just place some watermark randomly in an image? Does it make a difference? Continue reading “The Intuition Behind Image Watermarking”
Category: Image Processing
Digital Watermarking
 Let’s say you want to verify the authenticity of a signal. The signal can take any form like an image, audio, video, or any other kind of bit stream. By now, everybody would have heard the term “watermark” being used in the general sense. The most common example would be currency notes. Watermarks are embedded to verify the authenticity of the notes. But how do we achieve that with more complicated signals? As things move into the virtual world, where the threats are elevated to a much higher and abstract level, we need a way to verify the authenticity of different forms of digital signals. How do we do it? Continue reading “Digital Watermarking”
Let’s say you want to verify the authenticity of a signal. The signal can take any form like an image, audio, video, or any other kind of bit stream. By now, everybody would have heard the term “watermark” being used in the general sense. The most common example would be currency notes. Watermarks are embedded to verify the authenticity of the notes. But how do we achieve that with more complicated signals? As things move into the virtual world, where the threats are elevated to a much higher and abstract level, we need a way to verify the authenticity of different forms of digital signals. How do we do it? Continue reading “Digital Watermarking”
Image Steganography
 As discussed in my previous post, steganography is the art of hiding the fact that communication is taking place. We achieve this by hiding original information inside other information known as carrier files. Many different carrier file formats can be used, but digital images are the most popular because of their frequency of occurrence on the internet. For hiding secret information in images, there exists a large variety of steganographic techniques, some are more complex than others, and all of them have respective strong and weak points. Different applications have different requirements of the steganography technique used. For example, some applications may require absolute invisibility of the secret information, while others require a larger secret message to be hidden. How do we achieve this? How robust is it? Continue reading “Image Steganography”
As discussed in my previous post, steganography is the art of hiding the fact that communication is taking place. We achieve this by hiding original information inside other information known as carrier files. Many different carrier file formats can be used, but digital images are the most popular because of their frequency of occurrence on the internet. For hiding secret information in images, there exists a large variety of steganographic techniques, some are more complex than others, and all of them have respective strong and weak points. Different applications have different requirements of the steganography technique used. For example, some applications may require absolute invisibility of the secret information, while others require a larger secret message to be hidden. How do we achieve this? How robust is it? Continue reading “Image Steganography”
What Are Conditional Random Fields?
 This is a continuation of my previous blog post. In that post, we discussed about why we need conditional random fields in the first place. We have graphical models in machine learning that are widely used to solve many different problems. But Conditional Random Fields (CRFs) address a critical problem faced by these graphical models. A popular example for graphical models is Hidden Markov Models (HMMs). HMMs have gained a lot of popularity in recent years due to their robustness and accuracy. They are used in computer vision, speech recognition and other time-series related data analysis. CRFs outperform HMMs in many different tasks. How is that? What are these CRFs and how are they formulated? Continue reading “What Are Conditional Random Fields?”
This is a continuation of my previous blog post. In that post, we discussed about why we need conditional random fields in the first place. We have graphical models in machine learning that are widely used to solve many different problems. But Conditional Random Fields (CRFs) address a critical problem faced by these graphical models. A popular example for graphical models is Hidden Markov Models (HMMs). HMMs have gained a lot of popularity in recent years due to their robustness and accuracy. They are used in computer vision, speech recognition and other time-series related data analysis. CRFs outperform HMMs in many different tasks. How is that? What are these CRFs and how are they formulated? Continue reading “What Are Conditional Random Fields?”
Why Do We Need Conditional Random Fields?
 This is a two-part discussion. In this blog post, we will discuss the need for conditional random fields. In the next one, we will discuss what exactly they are and how do we use them. The task of assigning labels to a set of observation sequences arises in many fields, including computer vision, bioinformatics, computational linguistics and speech recognition. For example, consider the natural language processing task of labeling the words in a sentence with their corresponding part-of-speech tags. In this task, each word is labeled with a tag indicating its appropriate part of speech, resulting in annotated text. To give another example, consider the task of labeling a video with the mental state of a person based on the observed behavior. You have to analyze the facial expressions of the user and determine if the user is happy, angry, sad etc. We often wish to predict a large number of variables that depend on each other as well as on other observed variables. How to achieve these tasks? What model should we use? Continue reading “Why Do We Need Conditional Random Fields?”
This is a two-part discussion. In this blog post, we will discuss the need for conditional random fields. In the next one, we will discuss what exactly they are and how do we use them. The task of assigning labels to a set of observation sequences arises in many fields, including computer vision, bioinformatics, computational linguistics and speech recognition. For example, consider the natural language processing task of labeling the words in a sentence with their corresponding part-of-speech tags. In this task, each word is labeled with a tag indicating its appropriate part of speech, resulting in annotated text. To give another example, consider the task of labeling a video with the mental state of a person based on the observed behavior. You have to analyze the facial expressions of the user and determine if the user is happy, angry, sad etc. We often wish to predict a large number of variables that depend on each other as well as on other observed variables. How to achieve these tasks? What model should we use? Continue reading “Why Do We Need Conditional Random Fields?”
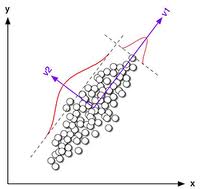
Derandomization Of RANSAC
 Let’s say you are a clothes designer and you want to design a pair of jeans. Since you are new to all this, you go out and collect a bunch of measurements from people to see how to design your jeans as far as sizing is concerned. One aspect of this project would be to see how the height of a person relates to the size of the jeans you are designing. From the measurements you took from those people, you notice a certain pattern that relates height of a person to the overall size of the jeans. Now you generalize this pattern and say that for a given height, a particular size is recommended. To deduce the pattern, you just took a bunch of points and drew a line through them so that it is close to all those points. Pretty simple right! What if there are a few points that are way off from all the other points? Would you consider them while deducing your pattern? You will probably discard them because they are outliers. This was a small sample set, so you could notice these outliers manually. What if there were a million points? Continue reading “Derandomization Of RANSAC”
Let’s say you are a clothes designer and you want to design a pair of jeans. Since you are new to all this, you go out and collect a bunch of measurements from people to see how to design your jeans as far as sizing is concerned. One aspect of this project would be to see how the height of a person relates to the size of the jeans you are designing. From the measurements you took from those people, you notice a certain pattern that relates height of a person to the overall size of the jeans. Now you generalize this pattern and say that for a given height, a particular size is recommended. To deduce the pattern, you just took a bunch of points and drew a line through them so that it is close to all those points. Pretty simple right! What if there are a few points that are way off from all the other points? Would you consider them while deducing your pattern? You will probably discard them because they are outliers. This was a small sample set, so you could notice these outliers manually. What if there were a million points? Continue reading “Derandomization Of RANSAC”
The Ramifications Of H.265
 The International Telecommunication Union (ITU) recently approved the next generation video format known as H.265, which would be the successor to the current H.264 standard. H.265, also informally known as High Efficiency Video Coding (HEVC), is supposed to be twice as efficient as H.264 in terms of compression. H.265 relies on the fact that processing power is increasing on our devices, and uses more processing power to achieve better compression. Now how will this affect our lives? Is this just an algorithmic improvement or will it have a tangible impact? Continue reading “The Ramifications Of H.265”
The International Telecommunication Union (ITU) recently approved the next generation video format known as H.265, which would be the successor to the current H.264 standard. H.265, also informally known as High Efficiency Video Coding (HEVC), is supposed to be twice as efficient as H.264 in terms of compression. H.265 relies on the fact that processing power is increasing on our devices, and uses more processing power to achieve better compression. Now how will this affect our lives? Is this just an algorithmic improvement or will it have a tangible impact? Continue reading “The Ramifications Of H.265”
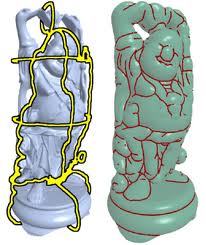
Curvelet Analysis
 This blog post is a continuation of my previous post on ridgelet analysis. Motivated by the problem of finding efficient representation of objects, people introduced yet another representation system called the curvelet transform. This is very efficient in representing objects that have discontinuities along curves, and compressing image data as well. Curvelets are a non-adaptive technique for multi-scale object representation. Why do we need this? Are they more efficient that ridgelets? Continue reading “Curvelet Analysis”
This blog post is a continuation of my previous post on ridgelet analysis. Motivated by the problem of finding efficient representation of objects, people introduced yet another representation system called the curvelet transform. This is very efficient in representing objects that have discontinuities along curves, and compressing image data as well. Curvelets are a non-adaptive technique for multi-scale object representation. Why do we need this? Are they more efficient that ridgelets? Continue reading “Curvelet Analysis”
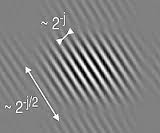
Ridgelet Analysis
 The pioneering work of researchers on signal processing paved the way to the powerful concept of multiresolution analysis. This is perhaps best known under the generic name of wavelets. Signals occur in the form of images, voice, radar, sonar, infrared etc. Different techniques have been developed over the years to understand these signals. Multiresolution provides us with tools to analyze these signals at different level of resolutions. It’s like looking at the same thing using a microscope with different magnifying powers. The formulation of multiresolution analysis moved the signal processing field away from classical Fourier analysis. But are wavelets equally efficient for all the shapes? Can we somehow take advantage of the shape of the object? Continue reading “Ridgelet Analysis”
The pioneering work of researchers on signal processing paved the way to the powerful concept of multiresolution analysis. This is perhaps best known under the generic name of wavelets. Signals occur in the form of images, voice, radar, sonar, infrared etc. Different techniques have been developed over the years to understand these signals. Multiresolution provides us with tools to analyze these signals at different level of resolutions. It’s like looking at the same thing using a microscope with different magnifying powers. The formulation of multiresolution analysis moved the signal processing field away from classical Fourier analysis. But are wavelets equally efficient for all the shapes? Can we somehow take advantage of the shape of the object? Continue reading “Ridgelet Analysis”
Principal Component Analysis
 Principal Component Analysis (PCA) is one of most useful tools in the field of pattern recognition. Let’s say you are making a list of people and collecting information about their physical attributes. Some of the more common attributes include height, weight, chest, waist and biceps. If you store 5 attributes per person, it is equivalent to storing a 5-dimensional feature vector. If you generalize it for ‘n’ different attributes, you are constructing an n-dimensional feature vector. Now you may want to analyze this data and cluster people into different categories based on these attributes. PCA comes into picture when have a set of datapoints which are multidimensional feature vectors and the dimensionality is high. If you want to analyze the patterns in our earlier example, it’s quite simple because it’s just a 5-dimensional feature vector. In real-life systems, the dimensionality is really high (often in hundreds or thousands) and it becomes very complex and time-consuming to analyze such data. What should we do now? Continue reading “Principal Component Analysis”
Principal Component Analysis (PCA) is one of most useful tools in the field of pattern recognition. Let’s say you are making a list of people and collecting information about their physical attributes. Some of the more common attributes include height, weight, chest, waist and biceps. If you store 5 attributes per person, it is equivalent to storing a 5-dimensional feature vector. If you generalize it for ‘n’ different attributes, you are constructing an n-dimensional feature vector. Now you may want to analyze this data and cluster people into different categories based on these attributes. PCA comes into picture when have a set of datapoints which are multidimensional feature vectors and the dimensionality is high. If you want to analyze the patterns in our earlier example, it’s quite simple because it’s just a 5-dimensional feature vector. In real-life systems, the dimensionality is really high (often in hundreds or thousands) and it becomes very complex and time-consuming to analyze such data. What should we do now? Continue reading “Principal Component Analysis”